Documentation Index
Fetch the complete documentation index at: https://mintlify.com/argoproj/argo-cd/llms.txt
Use this file to discover all available pages before exploring further.
Overview
Argo CD is designed with a component-based architecture that separates responsibilities into different deployable units. This design provides modularity, single responsibility, and reusability—enabling you to scale components independently and customize your deployment.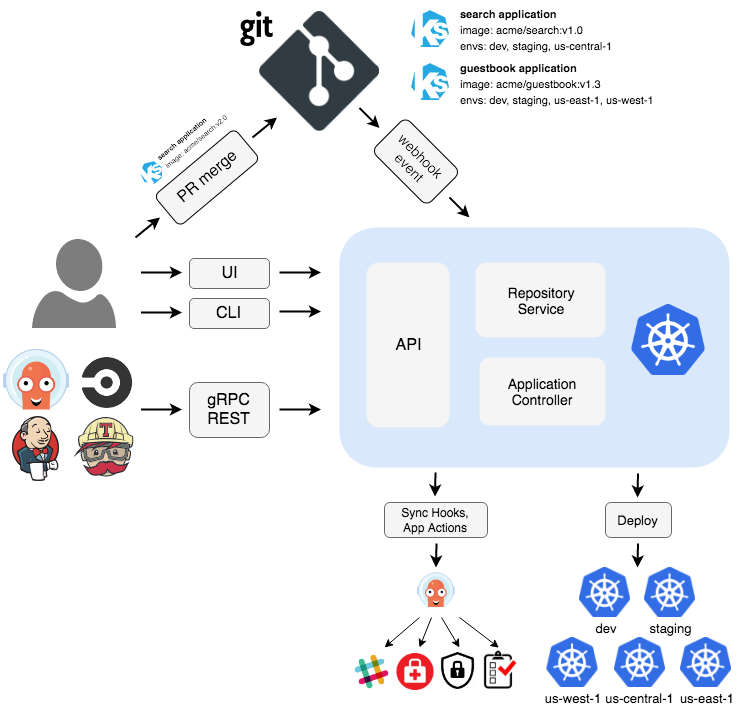
Core Components
Argo CD consists of several key components that work together to provide continuous delivery capabilities.API Server
The API Server is a gRPC/REST server that exposes the API consumed by the Web UI, CLI, and CI/CD systems. Responsibilities:- Application management and status reporting
- Invoking application operations (sync, rollback, user-defined actions)
- Repository and cluster credential management (stored as Kubernetes secrets)
- Authentication and delegation to external identity providers
- RBAC enforcement
- Listener/forwarder for Git webhook events
The API Server is stateless and can be horizontally scaled for high availability. See High Availability for scaling recommendations.
Repository Server
The Repository Server is an internal service that maintains a local cache of Git repositories holding application manifests. Responsibilities:- Generate and return Kubernetes manifests given:
- Repository URL
- Revision (commit, tag, branch)
- Application path
- Template-specific settings (Helm values, Kustomize parameters, etc.)
- Cache repository contents for performance
- Execute configuration management tools (Helm, Kustomize, Jsonnet)
Repo Server Caching
Repo Server Caching
The Repository Server caches repository contents in Redis to minimize Git operations:
- Repository metadata: Cached for 3 minutes (default)
- Manifest generation: Cached until repository revision changes
- Helm chart indexes: Cached for 24 hours (default)
argocd-cm ConfigMap:Application Controller
The Application Controller is a Kubernetes controller that continuously monitors running applications and compares the current live state against the desired target state. Responsibilities:- Monitor applications by comparing live state vs. target state
- Detect
OutOfSyncapplication state - Optionally take corrective action (if auto-sync enabled)
- Invoke lifecycle hooks (PreSync, Sync, PostSync)
- Reconcile Application and AppProject resources
ApplicationSet Controller
The ApplicationSet Controller automates the generation of Argo CD Applications using templates. Responsibilities:- Reconcile ApplicationSet resources
- Generate Application resources from templates
- Support multiple generators (Git, Cluster, List, Matrix, etc.)
Redis
Redis provides caching and temporary storage for Argo CD components. Use Cases:- Cache Git repository contents
- Cache Kubernetes API responses
- Store temporary data for UI operations
- Cache Helm chart indexes
- Store application controller state
Redis uses password authentication by default. The password is stored in the
argocd-redis secret under the auth key.For high availability, consider deploying Redis in HA mode with Redis Sentinel or using a managed Redis service.Dex (Optional)
Dex is an identity service that provides authentication with external OIDC providers. Supported Providers:- LDAP/Active Directory
- SAML 2.0
- GitHub
- GitLab
- Microsoft
- Okta
- And many more
Dex is optional. You can use alternative authentication methods:
- Built-in local users
- Direct OIDC integration (bypassing Dex)
- Service accounts for automation
Component Dependencies
The diagram below shows dependencies between components organized in logical layers:Application Layer
API Server - Provides capabilities to support the UI layerDepends on: Repository Server, Application Controller, Redis, Dex, Kubernetes API
Core Layer
Application Controller, ApplicationSet Controller, Repository Server - Core GitOps functionality
- Application Controller depends on: Repository Server, Kubernetes API, Redis
- Repository Server depends on: Git repositories, Redis
- ApplicationSet Controller depends on: Kubernetes API
Dependency Rule: Components in upper layers can depend on components in lower layers, but components in lower layers never depend on upper layers. This ensures a clean, maintainable architecture.
Data Flow
Application Sync Flow
High Availability
For production deployments, Argo CD supports high availability configurations.HA Deployment Architecture
Scalable Components:- API Server: Multiple replicas (3+ recommended)
- Repository Server: Multiple replicas (3+ recommended)
- Application Controller: Active-passive with leader election
- ApplicationSet Controller: Active-passive with leader election
- Redis: HA mode with Sentinel (3+ instances recommended)
Sharding the Application Controller
For deployments with thousands of applications, shard the Application Controller:Sharding Strategy
Sharding Strategy
Deployment Patterns
Standard Installation
Use case: Development, testing, small-scale production- 1 API Server replica
- 1 Repository Server replica
- 1 Application Controller
- 1 Redis instance
- 1 Dex instance
Namespace-Scoped Installation
Use case: Multi-tenant clusters, limited permissionsCore Installation
Use case: Lightweight deployments, no UI/SSO required- API Server
- Dex
- Web UI
argocd login --core.
High Availability Installation
Use case: Production deployments, mission-critical applications- 3 API Server replicas
- 3 Repository Server replicas
- 1 Application Controller (with leader election)
- 3 Redis instances (HA mode with Sentinel)
- 3 Dex replicas
Security Considerations
Network Policies
Network Policies
Restrict network traffic between components:
Monitoring and Observability
Metrics
Argo CD exposes Prometheus metrics on each component:- API Server:
:8083/metrics - Repository Server:
:8084/metrics - Application Controller:
:8082/metrics
Health Checks
Each component exposes health endpoints:Next Steps
High Availability
Configure Argo CD for production with HA
Metrics & Monitoring
Set up monitoring with Prometheus and Grafana
Disaster Recovery
Plan for backup and recovery scenarios
User Management
Configure SSO and RBAC for your team